Your WordPress website may become a victim of a data-stealing attempt or worse thanks to a vulnerability that got noticed in a popular WordPress plugin last week.
The plug-in that caused some kind of mayhem around for owners of WordPress-based websites was Code Snippet, which is a plugin for WordPress websites that allows users to run PHP code snippets in a much more convenient fashion. The primary purpose the plug-in brings to the users is that they do not have to go on and develop their own snippets and allowing less load on their sites. Not only that, this plug-in offers to clean the .php files that cause the site to slow down sometimes with much more ease.
The Bug in the Plug-in that caused Chaos among the WordPress Site Owners
Discovered by a world-renowned security firm called Wordfence, it was a bug inside the Code Snippet plugin that was capable of hacking the WordPress website and writing a new PHP code on it beyond the consent of the owner of that WordPress Website.
The newly induced code would allow the hackers to access the website and do whatever they want on it from controlling it remotely to spreading additional forms of malware on other platforms as well through it. The remote monitoring of the website through the bug in the plug-in refers to activities like changing the user’s site without their consent and stealing confidential information out of it. In short, it means taking complete administrative control of the website.
The Vulnerability in the WordPress Plug-In was a Small Breach in the Import Section
Despite the fact, the Code Snippet’s developers produced a reasonably secure plug-in for the convenience of the WordPress platform users, Wordfence’s research team found the bug in the import feature of the plugin, which was open enough doorway for hackers to infiltrate the site and wreak havoc in any way they intended.
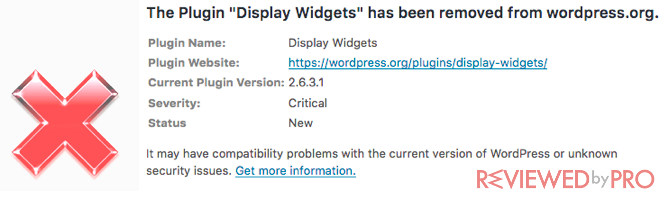
During the last week of January 2020, the bug issue was handled, and the original developers of the plugins fixed. Moreover, notification was sent to the users of the Code Snippet plugin that asked them to uninstall the already established version and update it to the latest one so that the gateway to the breach could be closed once and for all.
The Problem with The WordPress Plugin Update that was intended to Fix the Bug
There was one issue behind that if the notification didn’t reach some website administrator and they failed to update the plugin; then the site would remain susceptible to outside data hacking attempt as long as one could imagine.
This fact was made into a real concern when the plug-in developers released their most recent stats, which stated that out of 200,000 sites that owned the Code Snippet plug-in, only 55,000 sites were refreshed and updated to the latest version of the plug-in. It implied that a staggering amount of more than 140,000 WordPress websites were still under a hanging sword of data-stealing attack.
WordPress Site Owners Need to be More Vigilant and Active
A website is pretty much like a business place for the administrator, and it is their job to keep it safe and look for possible flaws within its walls(plug-ins) so that no one is able to hack their business ever. Given the popularity of the WordPress platform in the marketplace due to its being an open-source platform, it was sure to catch the eye of cybercriminals.
Much like any big player of their respective industry, there will be attempts at causing harm to the reputation of the platform and the belongings(data) of the users in various shapes and forms.
Several security firms verify this fact with stats showing that over 90% of data breaches caused on active websites of the world were due to their vulnerable state, which made the situation compromisable. The case was different for other content management systems (CMS) like Magento and Joomla sites, with less than 5% were accounted for each of them.
The key to keep the WordPress site out of the grasps of ill-intentioned people is for the administrator to remain vigilant and arrange for several preventative measures. Here are the ways to keeps your WordPress site secure:
- Keep the Plug-ins and themes updated – If you are an active administrator of a WordPress site and wish to keep it safe and healthy, then it is vital to stay on a lookout for new updates and features of all the plug-ins that you have activated on the website. It is also worth mentioning that you should always keep a list of each plug-in and theme installed on your website as sometimes these malware aim to hide in plain sight in the form of such plug-ins and carry on with their operation;
- Arrange for a WordPress Hosting Provider – It can get confusing for the admin to manage the entire website without any outside. A hosting provider serves such a purpose very well as it updates all the plugins of the WordPress website automatically and you wouldn’t have to worry about any data breach through the WordPress plug-in ever again;
- Always keep a lookout for Notifications – Although it is pretty common to ignore the visible signs of updating the plug-ins of WordPress to their latest versions, it is still irresponsible to not check the notifications sent by the WordPress support team about any possible data breaches or bugs within the platforms. These messages prompt the admin to update the respective plug-in to avoid getting hacked.
We have to Remain One Step Ahead of the Hackers to Keep WordPress Safe – Final Thoughts
Cybercriminals will never knock on your WordPress site’s door, asking for permission to infiltrate your data. They will always find possible breaches and vulnerabilities within the system to creep into your business and wreak damage, and they are showing no visible signs of slowing down.
It is why no time has been direr and severe than today to arrange for possible security things to keep WordPress website safe from such threats so that such criminals and their malware would always be playing catchup and never touch your site ever.




